Works for: Mac / Windows / Linux / Ubuntu
It’s not funny to have your computer stolen, it even sucks BIG time.
Not only “they” take your belongings, but also they often go away with your memories and personal information.
A home insurance will only refund you cents on the dollar: Once the package was open, your precious laptop took a bad hit on the blue book; probably 30% the first day. A month after, your superb machine is obsolete and the value went down like a beer in the throat of a thirsty Irishman..
As for the rest …your precious pictures, emails, documents… bye-bye ..But most important, the thief may have access to bank accounts, Social Security Number, Credit Card information, and you know it’s were it is going to hurt really bad: Changing and securing all this information: Call the bank, Call the CC company, etc etc. In short: Good luck!
So, what can you do beside adding locks, alarms systems and hiring a bodyguard?
You could hire a spy!
For less than you will ever believe, you could hire a spy.
For how much? Well, between $49 and Free
Free is a very good price …So, read carefully, very carefully…
Multiple solutions exist: LoJack for computers ($$$) Mobile Me (via Back to my Mac), Undercover ($$) & Prey Project (Free)
In this post I will only look at Undercover & Prey, LoJack being a little expensive and Mobile Me having a serious stealth issue in my opinion. (a "Smile you're being filmed" would have more discreet)
First, how is it working?
As soon as your laptop or desktop is missing (stolen or lost), go to the website of the respective company and declare your computer missing, lost or stolen.
This action will activate a software (must be installed PRIOR to the activation) and this software will log the IP address used, take pictures, screenshots and sometime Keylogging and send all of that to either: an email address or create a report on a website
You’ll end up (with some chance) with at least, few pictures of the thief, screenshots and his IP address.
I have previously mentioned in this blog what was IP tracing and Keylogging, as well as webcam & microphone remote control.
The IP Address being a very easy way locate someone, even for noobs like the rest of us. For Law Enforcement Agency it's a joke: they'll get everything and even more.
Fee or Free?
Undercover being a (one time) fee service ($49), it has some features that Prey does not have: Keylogging and a nifty simulation of hardware failure, furthermore, Undercover will contact the authorities for you and provides them with all the necessary information.
Prey is Free, but you are on your own and it does not have Keylogging capabilities, or Hardware failure simulation.
Both system have limitations, and there is no guarantee that you will recover the stolen goods, but you have a much greater chance with them than without.
The Undercover Website explains all steps very well, and as I know you: let's move on to the free one: Prey
Be very careful, Prey is not easy to remove under Mac OS (and it should not be!)
Step by Step How to:
Go to the Preyproject website: http://preyproject.com/
Top left, select your language
Sign Up and Create an Account (email, pswd, etc)
Wait for the verification email, and activate your account
Create a Profile, up to 3 Devices. i.e 2 laptops, 1 desktop
Note carefully the API & Device number
Download Prey

Double click to Install
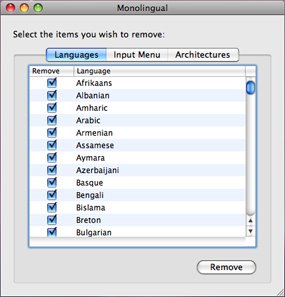
Select the Install option: Control Panel or Standalone

I would strongly suggest you
to use the Control Panel Option
Enter the general settings value, Timing and Language
Enter the API key and the Device Key (paste and copy from the website)
Important: Keep that for yourself!
Now that Prey is installed, go back to the website, log in and go to "My Devices"
Select a Device
Set up your Preferences:
Missing On/Off (by default is should be Off)
-But you are going to test it! Aren't you?
Auto update, Delay between executions, reports, etc
If your computer is not equipped with a built in webcam, the Webcam option is pretty much useless.
Action Module:
I would suggest to de-activate (Off) this option. A noisy pop-up appears and, in my humble opinion it has the only purpose of alerting the thief that something is happening.
I better have the chance to take few pictures of his face than letting him know that I am monitoring his activities.
Don't forget to UPDATE!
Don't forget to UPDATE!
WARNING:
It may take up to 15 minutes the first time you activate Prey to receive a Report Don't panic, be a little patient.
Depending on your screen size, the Screenshot can be large, hence it may take Prey some time to transmit the Screenshot and the picture. (which is smart: using all your bandwith at once could alert the thief that something is fishy...) I would also suggest to restart your computer after installing. It seems to me that it works better...
Pop Up Alert example. Bah!
Prey in Surveillance Mode

What if:
-You go on vacation for few days and come back to find your home burglarized?
The Thief may have visited you few hours ago, or few days ago..
If the villains just did it, it's Ok. Activate Prey and wait ....
But if they did it a week ago, your laptop may have changed hands few times and was probably re-formatted.
A solution is to leave Prey on "Surveillance mode" : just de-activate the webcam & screenshot option, leave the Network logging & use the max interval for timing.
Prey will log every hour, but will not take pictures or screenshot.
If a thief pays you a visit, you'll have the 10 last IP.
When you realize the theft, then you can activate Prey on "Attack Mode": Pictures, Screenshot every 2 minutes ...
Here are the setting for a "Surveillance Mode"

WARNING II
Prey will not prevent the thief to access your data and files. if you have stored sensitive documents and files in your computer you should read the post about encrypting your sensitive data. Seriously.
WARNING III
Prey will not work if the thief:
Does not use internet
Format the Hard Drive (Prevent that with a Firmware Lock)
Blind the webcam (no picture)
Uninstall the program (Unix command, no App is visible under Mac OS)
Limitations:
No Keylogging: Too bad, with a Keylogger and some luck, a simple search on social networks and you'll have all the info you want.
IP Address:
Will only give you the location of the connecting server. If the thief connects from a relayed IP, you'll end up with the location of the main server. (try tracing the IP of an Apple store, you'll end up with AT&T in Kansas..)
You can trace back the IP using an IP Trace Route such as explained in this post . Nevertheless, even without the perfect location, you'll have enough information to contact a law enforcement agency. (Law enforcement in the US need a subpoena to request data from an Internet Provider.)
Bugs
Unfortunately, the green led of the webcam will go on when it takes a picture; It is the only visible sign that Prey is on. (other than digging deep into your Mac)
IP Tracing Example (from a Spammer using a corporate bot. yup! Mac and Cheese manufacturing companies are spamming you with enlargement pills. ViaKrap??? ) Btw, I need reduction pills.

















No comments:
Post a Comment